Securely powering millions of connections
Trust Calendly to keep your data secure with enterprise-grade admin management, security integrations, data governance, compliance
audits, and privacy protections.
Simplified scheduling for more than 200,000,000 meetings
Market-leading software meets enterprise-grade security
Customer Data Protection
Domain Control and account oversight
Logical tenant separation
Encryption in transit (TLS 1.2+)
Encryption at-rest (AES-256) and in transit
Infrastructure Security
Hosted on leading cloud infrastructure provider
Network and perimeter protection
Application Protection
Web application firewall
Distributed Denial of Service (DDoS) Protections
Regular vulnerability scanning
Semi-annual penetration testing
Compliance & Privacy
SOC 2 Type 2 Report
SOC 3 Report
GDPR & CCPA compliance management
CSA STAR Level One attestation
ISO/IEC 27001 report
Org Security
Security education and awareness training
24/7 monitoring and incident response
Vendor risk management
Business continuity planning
Account Protection
Bot prevention
Login notifications
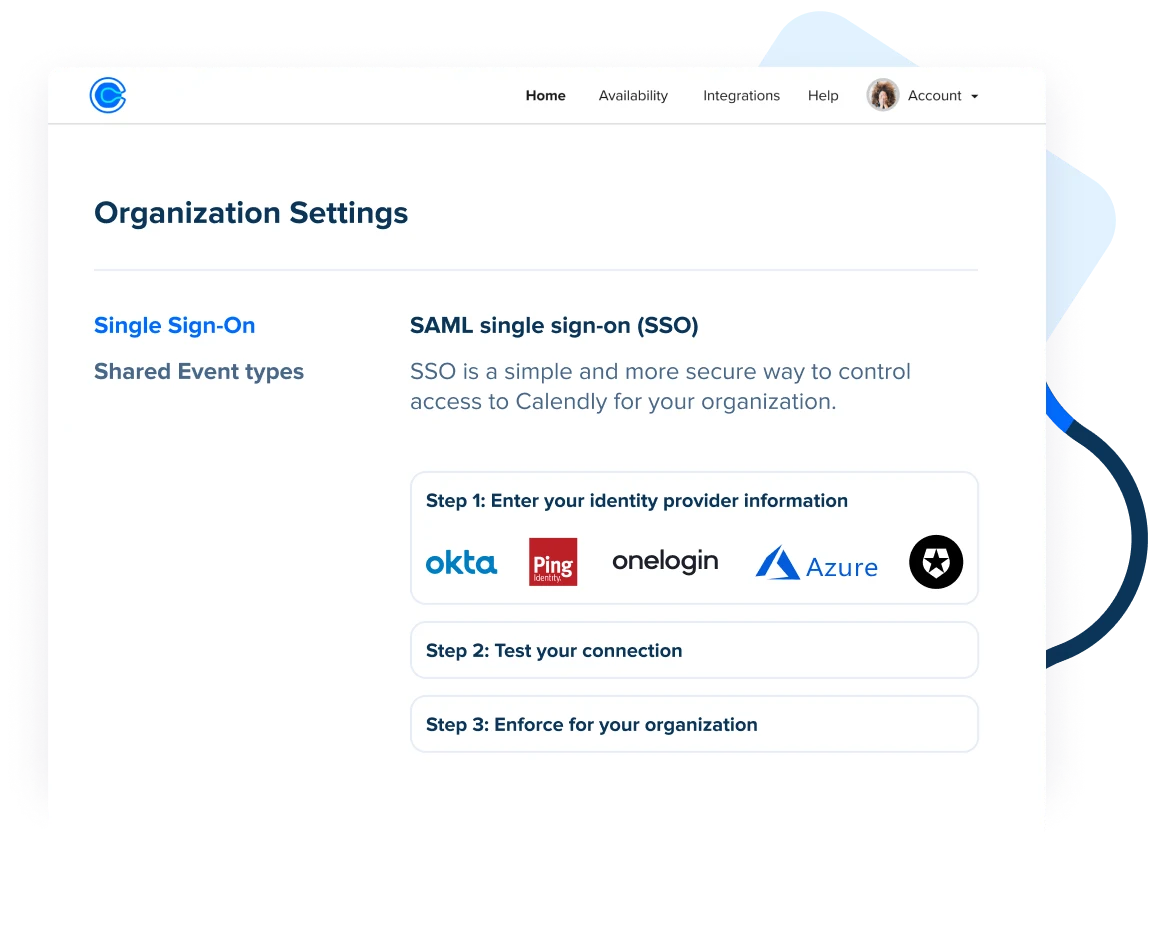
SSO and User lifecycle management (SCIM)
Real-time activity (audit) log
PII data deletion management
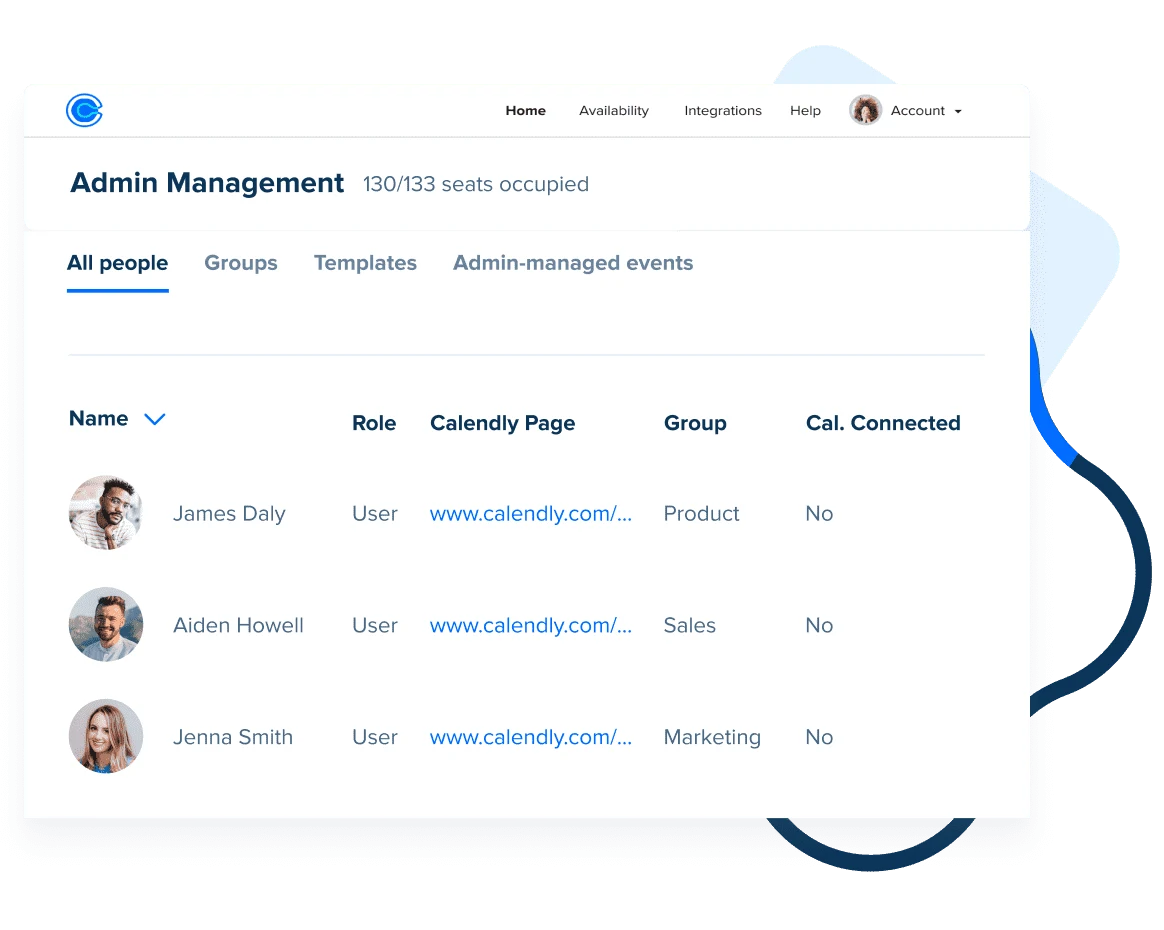
Flexible admin roles
Request documentation via Whistic
Calendly uses Whistic to securely share company and product security profiles as well as detailed documentation required for vendor security assessments.
Certifications and frameworks
Adapt to evolving business needs — without the risk
Security at scale
More people? No problem. Flexible access management tools fold seamlessly into your corporate policies and IT workflows so nothing falls through the cracks. Calendly offers SSO, SCIM, Domain Control, an activity log, and more.
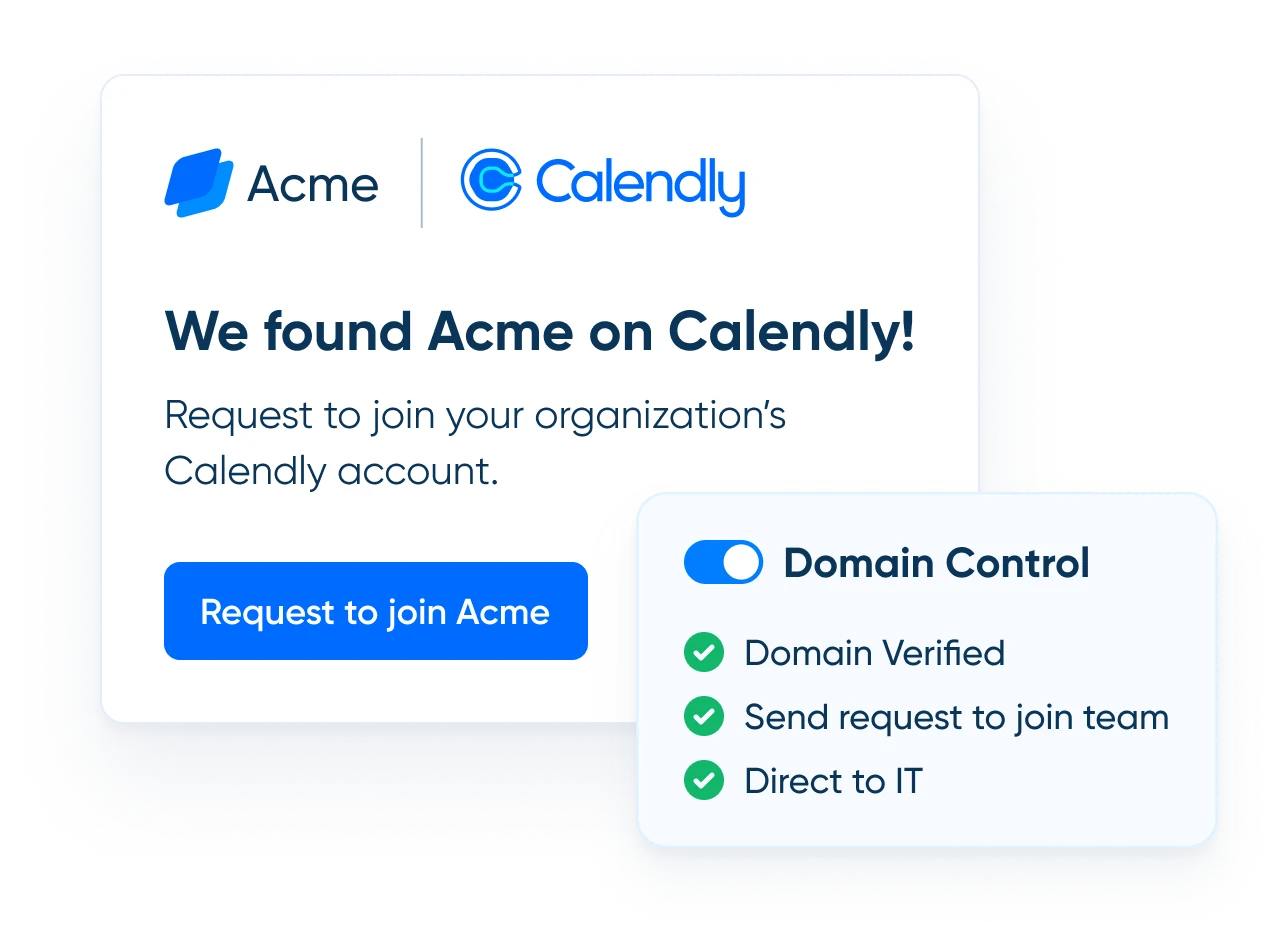
Domain control and data protection
Claim your corporate domain and establish how new employees signing up for Calendly request access to your centralized, IT-managed account
Collaboration with control
Empower your remote workforce to schedule efficiently as a team without adding risk to the business. Calendly's activity (audit) log offers visibility while granular, role-based permissions prevent unauthorized changes.
Enterprise-grade data governance
Maintain compliance with Calendly's governance and risk management capabilities — such as global retention policies, custom terms of service, data deletion, audit tracking, and more.
Fraud, Trust, and Safety
Security and the safeguarding of customer data shouldn’t be an afterthought. Calendly’s dedicated team constantly enhances our security techniques and addresses identity impersonation, fraud, and other suspicious activity.
“The security aspect of Calendly for enterprise was important and the ease of deploying it out to the people that needed it. We got over a hundred licenses and it was really easy to set it up and deploy it out to the people.”
Additional resources
Easy access for easy bookings
Share your Calendly link right from your browser, so you can schedule meetings without the back-and-forth.